Patriot Express Newsletter Edition #177
- Butch Erskine

- Aug 26, 2022
- 25 min read
Greetings and welcome to the Patriot Express Newsletter Edition #177. Thanks for joining us. We are always happy to have you join us. I would like to welcome our new readers and members. HFS continues growing as the world and nation spins out of control. Make yourself at home and give me a shout if you have questions or input.
As the weather changes and autumn seems right around the corner, have you started making plans for what to do for the autumn? Cleaning off your garden and begin preparing it for winter and spring is one thing to do. Cross checking your ready bag to rotate summer gear over to autumn gear depending on your location. Preparing your home with last minute winter needs such as bringing in firewood, cleaning your chimney, refueling your fuel tanks, and winterizing your auto's. Maybe stocking more food and needs as things get more stressful and more expensive. Do you have a winter checklist for your home of things you need to do? Now would be a good time to start writing things down.
We are looking forward to spending time this weekend with several local and out of town HFS members. It is always a treat when our HFS family comes together regardless of the location. Life is busy and hectic daily, but we must find time to stop and appreciate people who are important in our life. At the end of life when little else matters, our spiritual health, family and good friends will matter the most. We are always blessed to have this time together.
Moms, grandmothers, and ladies. One of our Patriotic Christian mothers reached out to me to share the below link to a really neat site titled Moms for America. I took a look at the site and its pretty neat with lots of information. If you are asking "what can you do to help reclaim the great nation, we love" then you will want to check this out. I want to think our Patriot sister from Central TN for sharing this information with us. Our thoughts and prayers are still with you, and we are always happy to hear from you. Home | Moms for America

As many gardens wind down from the summer crops and folks start planting autumn crops, We are still pulling cucumbers, tomatoes, sweet potatoes, and peppers.
We planted watermelon seeds this year we obtained from our HFS neighbor who shared a story about the seeds being 150-year-old seeds. The first month of growth was questionable if the plant would survive. Once the summer rains started the melon plants exploded with growth. Currently we have a few melons comparable to the picture to the left.
This is a picture of our first watermelon (Charleston Grey) picked this year. Weighing in at 33.8 lbs. We are blessed with so many treasures from our garden this year. Amen.
HFS September Travel Schedule -
Sept 10, 2022 - Huntsville, AL - Huntsville Public Library - 10 AM CST - Guest speaker at North Alabama Regional Preppers Network - Topic - Preparedness - Theory vs Reality
Sept 16 and 18, 2022 - Morovian Falls, NC - 7 pm and 10 AM - The Gathering, 976 W Meadow Parkway. Appearance supporting author John Dyslin - Nehemiah Strong. Will have a dinner on Friday around 430 with John for HFS members wishing to join us for the evening.
HFS Thursday Zoom - There was no event this week, however HFS sponsored a showing of the movie The Trance - The Cathy Obrien Story.
Communications: You can now follow HFS social media on the following outlets:
Facebook – Hope for Survival
YouTube Channel – Hope for Survival
MeWe: - //mewe.com/p/hopeforsurvival2
Odysee - Hope for Survival (odysee.com)
Parler - Preparedness101
Check out the HFS YouTube video at the following link. The most recent post is titled The Fence - What are you waiting for? Posted on Aug 10, 2022. If you have not, please hit subscribe and support our efforts to get the preparedness message out. We would like to see growth on the YouTube Channel platform. Thanks. https://youtu.be/nBGV832yUwA
Connect and give me a shout. Share with family and friends.
HFS will be recording a series of YouTube videos with author John Dyslin - Nehemiah Strong starting this week and you will be able to locate them on the HFS YouTube Channel as recordings are completed, edited, and posted. We are excited for this opportunity to give you an inside up-close look into John's thinking in writing Nehemiah Strong and his thoughts on today's church and the need for spiritual and personal preparedness. Video 1 is titled Spiritual Warfare Tool Kit - https://youtu.be/JcC7TXUyUUE Video 2 was recorded and is now posted on the HFS YouTube channel. Video 2 is titled Spiritual Warfare Tool Kit Applications - https://youtu.be/Pftjq1I7NRQ
Guest and Newcomers
If you are a guest or newcomer to the HFS journey, please check out this link for additional
information offered through HFS. https://www.hopeforsurvival.com/post/guest-and-newcomers-information-page
Hope for Survival books and HFS Thumb Drive for Emergency Documents -: You can obtain information on the two HFS books at this link: Survival, Preparedness, Disaster Management for individuals or family (hopeforsurvival.com)
Hope for Survival - How Food, Water, Shelter, and Security Could Save Your Life (Book 1)
Hope for Survival - The Mindset (Book 2)
HFS Thumb Drive for Emergency Documents - We just restocked the HFS Thumb drive and have them available now. Follow this link and you will see the add at the top of the page. Blog | Survival (hopeforsurvival.com)
We must make this brief public announcement to protect the innocent.
Ding, Ding, Ding....Attention HFS readers..... Opinions shared in this newsletter are just that, opinions, and nothing more. Read at your own risk. The owner and author of this site is not responsible for hurt feelings or thin-skinned readers. I do my best to show restraint and respect to the best extent possible. I take as many precautions as possible and try to remain as nonpolitical as possible, however, there are times when I just can't help but point certain things out. Occasionally I use words only Patriots recognize and understand. It's not personal against any non-Patriot. It's just the truth. Sometimes we must pull up our spenders and suck it up. Just saying. Stay the course, read what you want, and avoid the rest. Avoid fear porn as much as possible and the day will be okay. When all else fails… Keep the faith and always have Hope.
Let’s move along and get to some thoughts...
Thoughts for the week -
Security - It is important to try and have fun in everything we do. I like to joke that no one wants to listen to a security professional and believes everyone is a graduate of Donut University with a BS Degree in Bull Shooting. Then, they wake up and find a cow chasing the neighborhood bully through their front yard and they call 911.
My point here is security is a package of disciplines requiring numerous schools and training to perfect and understand how to apply the specific skill in the overall security took kit. Most won't realize it because to most, security is security. Think of it as a security filing cabinet and all the drawers are different pieces needed to make the security puzzle complete. I will caution that it is a puzzle in ways because you must decide which pieces will be used for the specific task at hand.
Risk Management Security Planning and Procedures ID/Authentication Access Control
Contingency Planning Audit Mechanisms Incident Response Encryption Mechanisms Security Awareness Training Boundary Protection (Hum/Tech) Physical Security Intrusion Protection Devices Personnel Security Security Configuration Settings Security Assessments Continuous Monitoring Exterior Intelligence gathering Internal Threat Two Person Buddy Teams Internal/External Communication Plan Boundary Protection Devices (Guards, checkpoints, technology, key logs, inventories)
I have spent the last 40 years working security, ant-terrorism, and emergency management related programs designing security plans and protecting planes, jets, Minuteman missile systems, funds, guns, people, special forces teams from all military services and missions around the world. This isn't a "toot my own horn" session because I quit the band years ago. At this point in life my attitude is this, if you are serious about protecting your objective then I'm here to help you. But if you want to look at me and tell me I'm paranoid when I tell you something you are doing is at risk, then please move along. What I am telling you is based on years of experience and things I can see as possibilities that you likely won't see. What has or hasn't worked. Trials and errors. Life and death.
The favorite line used is "nothing ever happens so why worry," or "I've never been attacked before so why worry about it?" Here is my theory, period. I look at something and I consider the basic threat of what you are doing and conduct a quick risk analysis against your odds. Nothing has ever happened, yet you continue leaving your purse on your car seat in a major city while parked at a local fitness center where you work out. You attend enough to establish a routine and other attendees recognize you and the vehicle you drive. Your car window is busted out and your purse stolen with all your cash and credit cards as well. You then express how hurt you are, and you just can't understand how it happened. Statistics, odds, and applied risk analysis predicted this would happen and you failed to listen. Remember, it was you who said, "nothing ever happens." Exactly, and dead people have never been dead before either. YOU are either ignoring, accepting, or mitigating threats every day.
Let's be as simple as possible here, the dog cage has a sign hanging on it that says, "DO NOT PET THE DOG" and every day you walk by the cage and notice the poor dog being alone in the caged prison. Finally, after several days you feel sorry for the dog and walk over to pet the dog's head. The dog jumps up and bites your arm off before you can pull your arm out and yell for help. I bet this never happened before, huh? You roll the dice, and you must live with the outcome. The posted sign was your warning. Just as crime stats and a risk assessment will identify potential risk involved, it is up to the person to heed, adjust, and mitigate the threat.
Most often the risk is not seeing the threat coming at you, but an alert to tell you of the possibility at a particular level. It is up to the individual to decide what route to take through mitigating steps or else changing the plan completely. What? Let's say you have 30 minutes each day to get from work to pick up a child at day care. You can't afford any delays or stops along the route. One day while driving the route you see road signs stating upcoming bridge repairs starting in a week. This could delay your timing to reach your child by the 30-minute point. The delay becomes your risk. You now know the threat to this objective is not reaching your child on time. You look at the area and decide to detour around the bridge to still make it to your child by the 30-minute targeted time. In the risk-analysis process you identify bridge work as a possible threat to achieving the time you need to reach your child. When you decide to alter your route and achieve your objective you are mitigating the threat of not making it on time. If you figure out you can't make it on time regardless of route and then pull your child from that particular location, you are mitigating the threat by deciding the plan won't work and the bridge repair is no longer applicable to your risk cycle.
I will try to walk you through the basic framework of security in the short space here. I will give you a couple concepts to always apply and you will be steps ahead of most. You can't just apply a security system to your house and be protected. Yes, you are safer because you now have early warning, but it is at your door, window, or inside your home. Add exterior sensors and cameras and you have now pushed your early warning a distance from your front door. This bought you some time. Add sensors and cameras to your fence line and you now have even more early warning and the building of what is called a layered security approach and defense in depth. This is put in simple terms because not everyone has dealt with security concepts in life. These layers can be human, physical, and technology-based resources, barriers, and alerting mechanisms.
Here is the Risk Assessment process to consider:

Even after you run the risk management cycle, you must continue to monitor, adjust, and run the cycle as often as needed or when a threat changes to the given task. It is an evergreen process.
Once you conduct a Risk Assessment of your location, you need to start documenting all areas assessed and your findings. You will want to track each item, progress achieved with the item, what you decide to do with the item (fix, mitigate, or alter your plan), and who is tracking the item. This is a sample. (Most people totally mess up by not doing the Risk Assessment steps).

The 5 D's of Security. Now this is different from 5-Guys Burgers. This is 5 D's of Security. If you can remember, understand, and apply these basic principles in all security applications, you should be in good shape. Let us get started.
The Five D’s - Deter, Detect, Delay, Deny, and Defend
The Five D’s of Security are common practice with military, police, and security forces, but the principles behind it can be used to keep you, your loved ones, and your teams safe.
1. Deter - First, a building or area must be sufficient to deter unwanted intruders attempting to receive access. Deterrence can be accomplished through making the facility tougher to enter, with parking lot barriers, access cards, and physical or technological security. This is the hardening of whatever you are trying to protect.
2. Detect - If deterrence fails, a system must ensure prompt detection that an unwanted intruder is present. Whether that be the emergency panic button system bank tellers have to silently alert their management and security or a loud fire alarm, a detection system will notify teams of a possible threat immediately. If your system is monitored 24 x 7, the alarm notification does not always have to be audible and can be a silent alarm.
3. Delay - After detection, security systems and personnel must delay unwanted intruders from gaining unauthorized access to your areas you are protecting. This could be your home, food storage location, area for keeping your animals or garden, medicine storage, ammunition and firearms, and any area of value. If possible, it would be best to start the delay tactic at your outermost perimeter once detected. Delays can include physical barriers such as entry points and hallways in apartments or barriers, fences, and gates at your outer most security-in-depth location. Delaying the threat would allow your security plan to be elevated and a response force put in place or to delay until other groups you have secured mutual agreements with to respond and help defend your area.
4. Deny - Should delaying an unwanted intruder fail, deny access to your areas being protected until a responder arrives. There are manual door reinforcements that can be used to safely secure people from the inside of a facility using plastic, metal, and even wood. If door reinforcements are not available, you can stack tables, desk, or computers, wrapping electrical cords around the door to create a makeshift lock, or any other form of barricading yourself safely from the intruder. This could be to your home or your safe room.
5. Defend - If the first four D’s can be implemented, the last D rarely comes into play before any type response arrives. In many cases a security element can safely secure the perimeter and begin to isolate the unwanted intruder, then remove them from the premise. If you find yourself in a situation where you need to defend yourself, your family and group, you can use anything small or large to defend yourself. This is where it is important to understand your weapon capabilities and using them in offensive and defensive measures. This should all be understood and decided in your planning phase. Non-lethal weapons may be your best bet initially, especially if sound discipline is critical. Other daily objects that can be used for defense in an unwanted intruder situation could be mace, pepper spray, a Taser gun, a bat, stapler, or coat rack.
If you can apply the five D’s of security to your security planning, it should give you a basic framework to build your security plan around. This will be covered as you continue reading. Remember, these are the steps to keep you alive and your security plan should identify how you plan to do it. The plan must be “evergreen” and adjust to situations you face. Flexibility is key.
Anyone can use and apply the Risk cycle with the FIve D's of security to lay out a security plan. It can be a basic plan to a complex plan. That is a personal choice. You can apply this concept to urban apartments, suburban neighborhoods and rural farms. A key in this process is to step outside the box and think like a bad guy. No one knows your plan and vulnerabilities better than you. How would you attack yourself knowing your strengths and weaknesses? Think hard target. You want to harden your location, your routines, and plans to deter any human threat from spending time deciding how to attack or hurt you. Remember, you are living your life day to day with routines and responsibilities. The bad guy has far more time to watch you from afar and figure out where you are weak. Change up your routines to be less predictable.
Here is a basic concept of what you should attempt to achieve when designing their security plan for a property. This can be an apartment, suburban area, or rural farm. You can use this for a community just as easily. You simply use Google Earth or another application to identify the total area in your community, find the center of the community and then use the Snip It tool to copy the picture and safe it. Then start using overlays to build the concept below to your community. This takes work and time, and most are not willing to dedicate the time to do it. I will ask you a simple question. What is your life, family, and community worth to you? I can't answer that question for you.

Each of the circles represents a barrier and as you close in to the inner most circle each level will require tighter controls and restrictions. Your greatest asset is your people and then your resources such as food, water, medicinal and protection. Remember, threats can be external and internal to your community or family. You must, I repeat must use internal controls to maintain control of your resources such as food, ammo, food, and medicinal products. Also utilize a two-person policy for individuals identified to access storage areas where you keep these items. Key control logs and rosters of individuals is a must to know who accesses these items. Don't fail in these areas.
You must be creative when determining what barriers, you will use and how to deploy them. Fences, downed trees, gates, vehicles, natural landscape, doors, alarms, cameras, stacks of tires, are all possible choices depending on your location and available resources on hand. You want to keep any possible threat as far away from your High Security Zone as possible. Early deterrence and then identification is your goal. The sooner you identify a threat the more time it will allow you to implement your plan on how you will deal with it. This is where having a community team works greater than a family living alone. When designing your circles (in theory) around your layers you want to design it to use your strong points to your advantage. Your goal after early detection should be to push the threat to your strongest point of approach to then utilize your designed defenses to eliminate the threat before it gets closer to your most protected areas.
Let's suppose you are working in your yard or farm and threats surface at your outer most perimeter. How will you alert your family and/or your community team? If you have a community team, the alert should be sounded at the outer most point. If you do not have a community team to sound the alarm, the first family member to see the threat will sound the alarm. What are you using for the alarm, and do you have an alerting system designed, set up, and understood by those on your team? A bell or an air horn will work great if your terrain isn't to spread out. If it is, you need some level of a system to get the word out fast. Maybe a phone app such as Signal or Zello. What can be used will be determined by what is available at the time of the event.
Here is a sample alerting matrix showing the concept I'm speaking about.

Security is a critical step in your daily life. How you approach everything you do will mean the difference in the outcome. While many are focused on the global and national threat of all the negatives and things impacting life from afar, don't forget to focus on your local area. Statistically speaking, the highest likely threat will be within one mile of your location. If Washington raises taxes, you feel it at your local level at home, your neighbors and local business owners. Fuel prices rise, you feel it locally. Elections are most often focused on the federal and state levels; however, your local elections are equally critical. Get involved and participate. Identify and get to know your local Sheriff. How does your Sheriff lean politically? What is your Sheriffs view on the Constitution and your rights? IS your Sheriff available for you to meet and talk and are you available to support your Sheriff when called upon as a citizen.
Again, set yourself and your home up to be a very hard target. If I am the bad guy out looking for a possible target, here are a few things I am going to look for in a home and community. High dollar homes and cars, electric cars/trucks, political stickers on the bumpers are good starters. A bumper sticker leaning left or right tells me a lot. Homes with open garage doors and side gates left open. Mailboxes with several days of mail packing the box. Paper boxes full of papers. Flags flying from post or front porch beams and what symbols the flag signifies. Once a home can be labeled a potential soft target, I would monitor routines for patterns used such as daily routes and stops at convenience stores for papers and coffee. Does the potential target drive the routes daily or frequent the same location for lunch. Why? If the home offers a higher degree of risk and the individual is the target, it may be easier to target the individual away from home vs at home. It all depends on the desired reason for targeting. If I want resources, then I must surveil the home vs the individual aside from possibly knowing when the home is empty. You can take several simple steps to rectify what is mentioned above. Help yourself out and work to be a hard target and unpredictable.
Lesser degrees of skills and mindset of the threat will likely mean they do not have the skills to conduct surveillance and opt to conduct their strike at any time desired. During a SHTF period it likely won't matter if you are home or not. As crazy as it may seem, a bad attitude, hungry stomach, and ego, will push the threat forward towards the objective without any consideration to being caught. When this is the case, if you have practiced the five D's of security it will hopefully allow you to have early detection of the threat and stop it before it is within your security zone, this being your home or protected resource.
Urban, Suburban and Rural locations must determine where they will get alternative water sources if their primary goes down. How far is it from the home or apartment? How will you transport the water from the location to the home. Will you be alone and if so, how will you protect yourself while in transit to and from the water source? Do you have responsibilities outside the home such as feeding animals or tending to a garden? What is your security plan for these locations? All of these questions must be addressed with a risk assessment and mitigations determined for all threats. How and where you are vulnerable could be the difference between living to see another day or losing everything you own, to include your life.
This is just a brief overlay to a broad security concept. I would encourage you to read both my books to get a better understanding of the big picture. I do hope to release a 3rd book soon that is on security in its entirety. Are you ready?
If you would like greater detail on this topic please see my YouTube video at this link:
You, your effort, and understanding of defending your property will be the likely difference of success or failure.
Next....
Fear - As each day passes, I encounter more and more people living in fear. Why? Is it not knowing what tomorrow brings? Fear of the unknown with all the craziness taking place around us? We, as humans, especially Americans, prefer to be left alone and to control our own day and way of life. Are we spoiled? Absolutely. We are Americans. I'm one of them but we often reach this choice and desire for different reasons.
I, for one, lived outside the United States for several years during my military years and visited and worked in over 50 countries on multiple continents. I witnessed third world life, starvation, death by warlords, poverty, destruction to the people by foreign enemies, petty crime by people against their own neighbors and more. Yes, each time I returned to America I got on my knees and thanked God for my nation and safety while away. I knew I was blessed to live in the greatest nation on earth. It is a simple fact. During this period of history our nation flew the flag with pride and unity. We had little human strife of people against people. We had political differences but still felt both parties represented the interest of the nation and its people.
Today, less than 20 years later, it is all different. No longer do I believe both political parties represent the best interest of our nation. We have roughly $260 trillion dollars in unfunded debt liabilities. We no longer offer an industrial backed nation. We make nothing. Our borders remain open and unvaccinated non-citizens roam our streets and schools. People are confused and untrusting of authorities. Family-owned businesses are being force closed by our government. Citizens would rather stay home for a check than work for a check. Children are taught a new history unlike what we learned. Statues representing our history are being wiped off the streets. Hollywood and sports figures seem to carry more authority and influence than pastors and local authorities. Citizenry are flooded with media and untruths. Crime is off the charts and educated authorities believe criminals should walk free to commit more crimes. Universities are no longer higher institutions of education and learning skills but instead politically driven and money pits. Adults are taking advantage of our youth and physically mutilating their bodies for profit. State governments are pushing laws to aid in adults abusing children sexually. While all of these things continue occurring, global powers are driving the depletion of farming and food for the masses. Technology is being used to imprison citizens and take away their constitutional rights. Psychological psychosis kidnaps the minds of many while they are paralyzed to what comes next.
People forget who they are and what they stand for. Churches no longer preach scripture and cater to make attendees feel good and draw their donations. While some advertised churches preach members can be their own god, other former church goers are leaving in masses and forming home groups. The church was once the respected voice of a community and included in local decisions and growth, the 501C3 movement has cowered the church's ability to preach the Gospel and speak as one voice to right and wrong. Today the remaining voices are labeled anti, racist, homophobe anti LGBTQ citizens.
Fear has kidnapped the majority and they no longer believe they have the power to standup against the minority and tell them enough is enough. They have forgotten the same scripture learned over years that condemns fear. They opt to leave the path of their Biblical guidance and step into the pits of evil amongst us opening up their personal armor to demonic attacks, all the while not realizing what they are doing
Until the majority of the masses wakes up the minority will continue steamrolling through our civil rights, personal freedoms, and way of life over the history of our great nation. We can complain all day and all night but until we have decided enough is enough, nothing will change. But it won't be so simple to defeat what is before us and ahead of us. It didn't happen overnight and defeating this evil empire will take strength, time, prayer, and effort. The question is, will the majority have the strength to stand strong and tall for the duration ahead?
When food becomes a weapon of choice by the authorities, how many of the majority will sell out their family, neighbors, and friends for a meal? When food is distributed along the lines of voting statistics and delivered to those who supported local candidates, how many of the majority will give in to obtain food for a hungry child or spouse? Who will withstand the minority and standup for the foundation of our faith and nation? Time will tell but, in the meantime, who is prepared to sustain this period?
Festus and I spent thousands of hours between 2010 and today researching, tracking, and following what we are seeing roll out today. From Agenda 2021, Wilderness Corridor, to digital currency, global currency to a global government. From sustainable developed cities to food shortages. We have sounded the alarm and continued to try and open minds and ears. Those who heeded our call over the past years will be prepared better than 95% of our population. And even then, it won't be easy. We laid out a structured plan going forward to help build a preparedness platform and program to help individuals, families, and communities. This included books, training platforms, YouTube videos, local assessments of properties, and more.
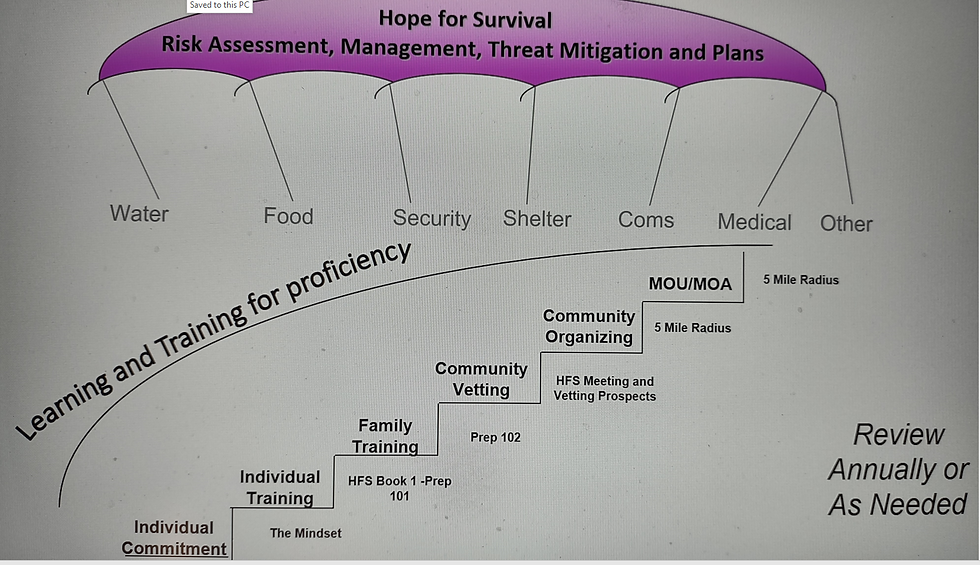
Below is a basic diagram of our approach.
Even through a structured and formatted approach, fear will remain with many because of the unknown. But, through faith, self-sustainment and self-reliability, many will have the ability to survive the unknown ahead. Government changes, civil unrest, local, state, and federal collapse, family division, economic failures, medical system failures, possible grid failures, and more, having the ability to provide for your family will be the difference in your survival.
Being prepared will not provide many answers to what is next, but it will provide in the two most important areas. That being food and water availability. While the world currently races to find food for their masses, you will be able to know you have a meal for the foreseeable future. What choices you make today to prepare will make the difference in your home and community. Knowing your neighbors also prepared will provide some relief because your neighbor and friend won't be beating on your door asking for food. You won't have to decide to turn your friend away to prevent taking food from your loved one.
I used to say the writing was on the wall, what are you waiting for? What I am saying was true all along and many called it fear porn trying to scare the masses, is now a reality. Today, the writing is all around you. You have a choice.
Until next week, be at peace and know each of us can make tomorrow a better day for someone else.
And that's my thoughts for the week....
Preparedness News –
1. From Sarah Anne Carter - The Survival Mom - 28 Pieces of Pioneer Weather Wisdom - Survival Mom (thesurvivalmom.com) - With winter quickly approaching any news or recommendations to help us better prepare is a plus. Some farmers are saying we are in for a cold wet winter. Time will tell.
2. From Old Garden Farms - How To Help Late Season Tomato Plants - Reviving Dying Plants! (oldworldgardenfarms.com) - It is mid-August and folks tell me their tomato plants are out of gas and dying off. Some preparers say they didn't get a good crop this season. We planted four tomato plants this season in our raised beds and had an enormous quantity. We have canned and frozen a large quantity and passed off others to neighbors. I'm hoping to keep the plants alive and producing until the first winter freeze.
3. From Fabian Ommar - The Organic Prepper - 15 Handyman Kits the Self-Sufficient Prepper Needs - The Organic Prepper - I don't know about you but I love articles with multiple suggestions on better ways to do things. Great items for my paper library. I purchased a book titled No Grid Survival Projects - How to produce everything you need on your property by Michael Major, Amber Robinson, Claude Davis and James Walton. I would recommend it for your book collection. Good stuff.
4. From Michael Major - Ask a Prepper - EMP Prevention Plan: Why Our Government Has Done Nothing (askaprepper.com) - Considering the minimal estimated cost of $40 billion dollars to fix the vulnerabilities against EMPs and CMEs compared to the post EMP/CME cost, one must wonder why after 25 years of warning and identified vulnerabilities, what is holding the government back from fixing this problem.
5. From Dennis Howard - Survival Cache - Emergency Radio Frequencies Every Prepper Should Know - Survival Cache - How and with what do you plan to obtain emergency information broadcast if the grid goes down and the nation goes to survival mode? Have you thought about it?
Other News -
1. From John and Nisha Whitehead - The Rutherford Institute - The Rutherford Institute :: Weaponizing the Bureaucracy: Who Will Protect Us from the Government’s Standing Army? | By John & Nisha Whitehead | - Are you ready to admit each day you wake up you see a nation you no longer recognize? It is a quicksand scenario most are missing because they await the attacking Army coming over the hill. The major question is who will come to rescue you? (Thanks Festus for this submission)
2. From Officer Tatum - Need to Know News - Armed IRS Agents Simulate Assault on Suburban Home. Leaked Video Claims to be IRS Training. (needtoknow.news) - I don't know but every time I think of the IRS agents, I think of the old Paul Simon tune "Somebody is knocking at your door." I believe his song is a bit happier than the reality here. Is there a truth or possibility this is why so many liberal cities started defunding police departments a few years ago? I do believe in politics no effort is without a cause and most are political without the consideration as to what is best for our great nation.
3. From Victor Davis Hanson - American Partisan - Victor Davis Hanson: The Left Accuses The Right Of Undermining Democracy While They Are Doing Revolutionary Things - American Partisan - Surprised? Remember hearing "never let a disaster go to waste?" Yea, well, guess what? You still have no eyes on the target or voice screaming timeout.
4. From Patrick Byrne - Deep Capture - Sean Stone and I Discuss: “Nationalism vs. Globalism” – Deep Capture - Great discussion. Does any of this information sound familiar to what you see and hear taking place in America today?
5. From Baxter Dmitry - News Punch - UN Declares War on 'Dangerous' Conspiracy Theories: 'The World Is NOT Secretly Manipulated By Global Elite' - News Punch - Well if this isn't a Grade A BullShot Sandwich nothing is. Imagine an elected leader taking a tour through a company within their district. The workers and shined and polished for the visit and the elected official is 30 minutes late. The workers stand awaiting their chance to get in a possible picture while explaining why their product is important to the nation the elected officials is employed by. The worker identifies by name with pride as the official smiles and states the importance of the job being done. A day later the worker encounters the elected official in a local market and approaches with a smile. The elected official has no clue who the person is. My point is we are fodder to the elite and those elected to all platforms. They have forgotten us and this is the start of the problem.
Drum roll...........
That's all my Patriot brothers and sisters.
Prayers - Please keep our great nation, our elected leaders, military and first responders in your thoughts and prayers. We pray for good health and wisdom. Please pray for our leadership to find answers and guidance to the problems facing our great nation. May your faith remain strong and answers to the unknown provided. God is good and may our prayers blanket and protect you and your circumstances. I pray for each, and every one of our Patriots.
May we pray for all the blessings and things in life to be thankful about and continued hope for revival around the world. We must continually pray for the unsaved, our family and friends who live each day without the protection for eternal life and salvation.
Please pray for our HFS family. I'm sure folks would appreciate it much. Please keep our Patriot brother and his family in northern Alabama in your prayers. We give thanks and praise to God for the safe travel and mission of our HFS families son traveling abroad. Thank you Lord). Please pray for our sister and brother in Central Alabama who is battling Covid-19 at this time. As time moves forward through all the unknowns, life continues which means sickness, personal issues, and family losses. We must continue uplifting one another daily.
As Patriots we must stay strong and never give up. Our home, community, and nation need us now more than ever. Stay focused on your local community and things that will impact you around the nation. Don't allow the events around you to create fear in your life. Build your own self-reliance and focus on faith and hope. Remember we are a blessed nation, and we must continue to be great people today and make a better tomorrow. Keep charging.
Blessings,
Bravo Echo Out,



Comments